SVME
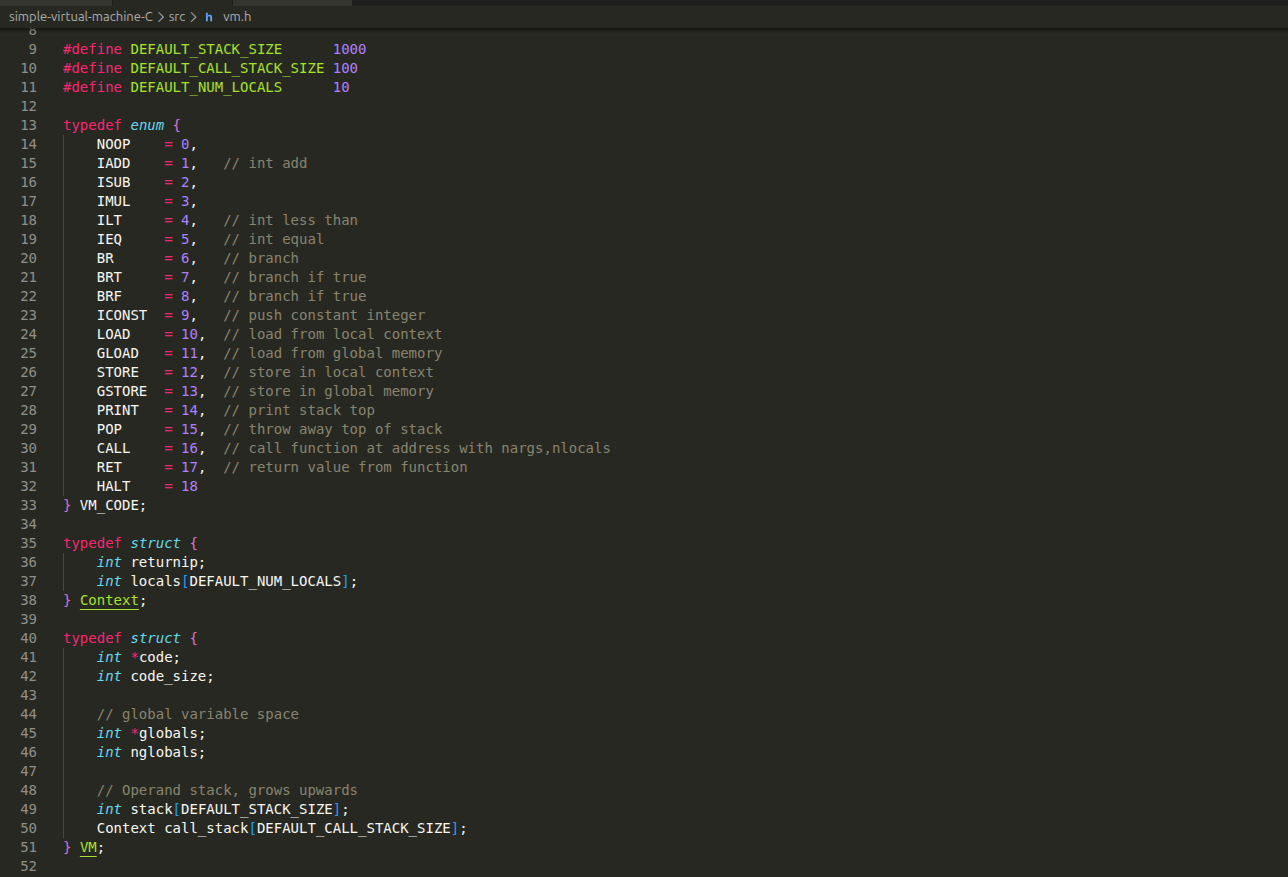
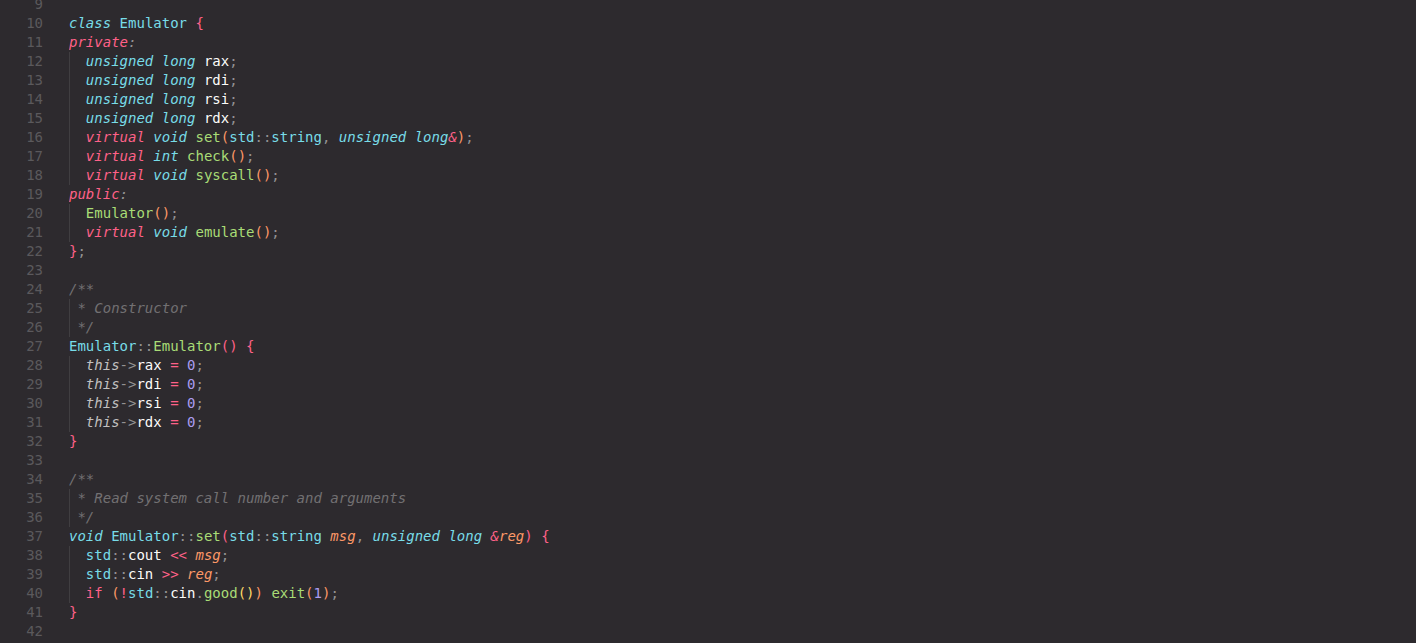
Real World CTF 4th - SVME Overview Challenge Name : SVME Author ; un1c0rn Description : “Professor Terence Parr has taught us how to build a virtual machine. Now it’s time to break it!” ...
Real World CTF 4th - SVME Overview Challenge Name : SVME Author ; un1c0rn Description : “Professor Terence Parr has taught us how to build a virtual machine. Now it’s time to break it!” ...
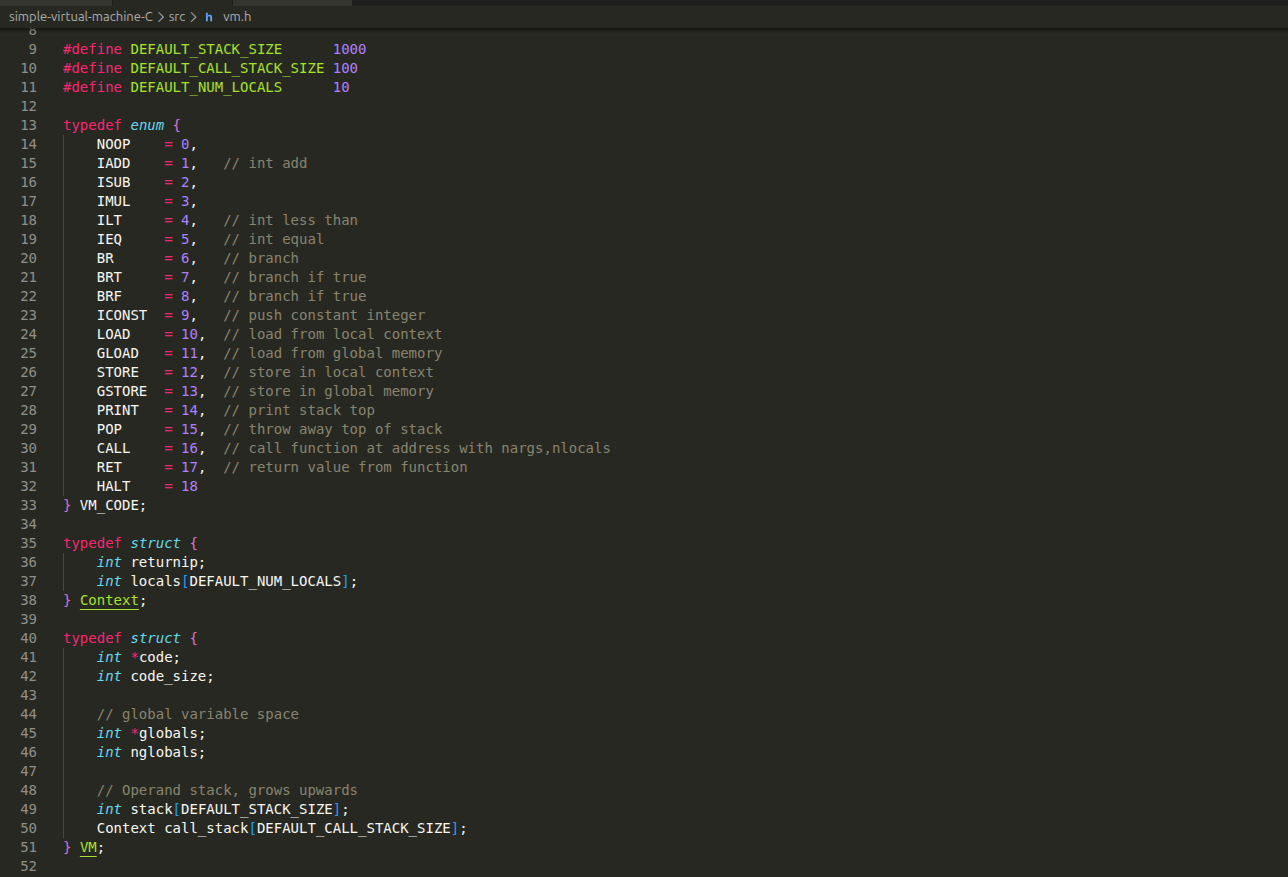
zer0pts 2020 - Syscall Kit Overview Syscall Kit is a hard rated pwnable challenge created by ptr-yudai. It is simply an emulator written in C++ that’s used to execute user-provided system calls....

CSEAN CTF 2026 Overview CSEAN CTF has concluded with 9 web challenges released. Here are my writeups as the author for some of them. CNotes Challenge Name : CNotes Description : Online ...
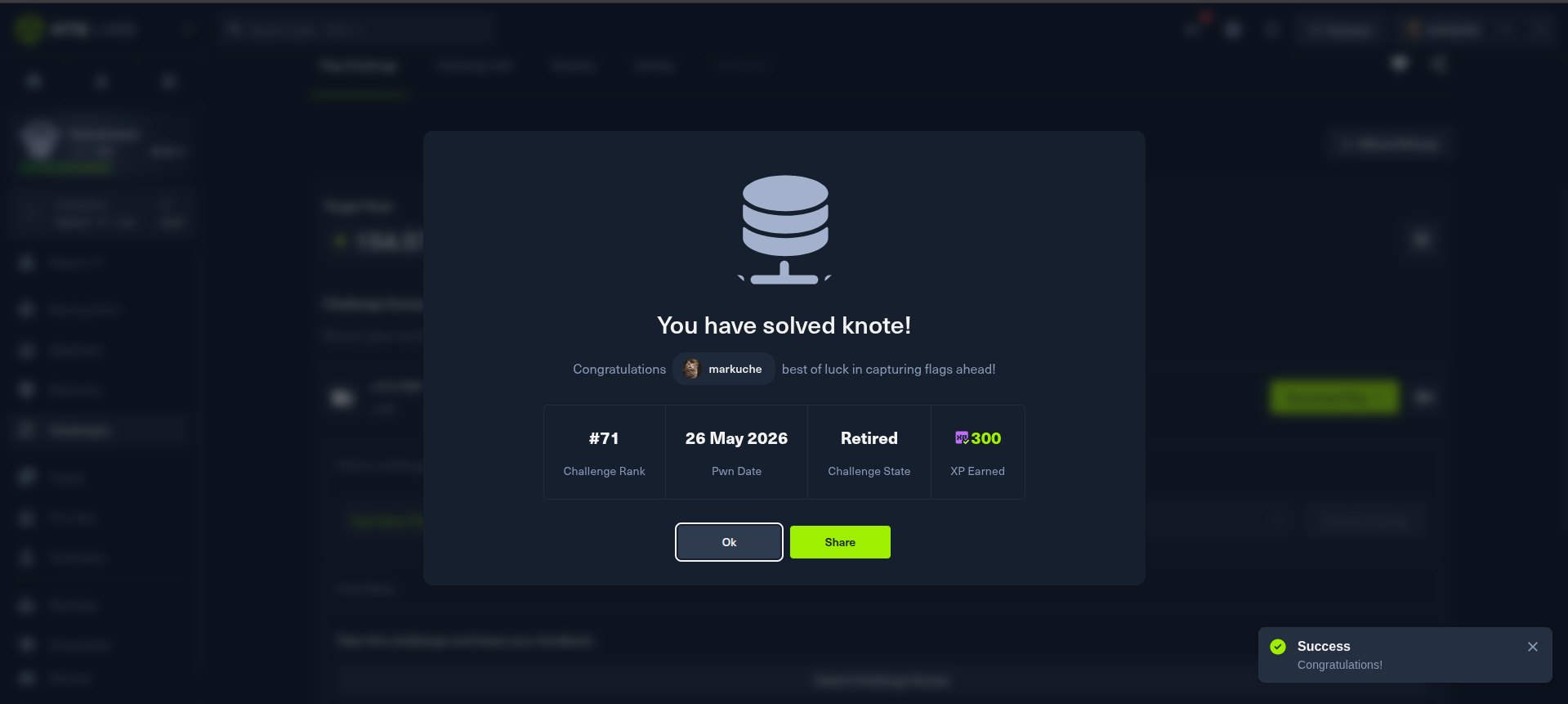
HackTheBox - Knote Overview Knote is a medium-difficulty kernel pwn challenge focused on exploiting a Use After Free to gain LPE. It’s a classic heap note challenge but in the kernel. Program A...
CSEAN CTF 2026 Overview The (CSEAN) held its annual Cyber Secure Nigeria 2026 Conference in Abuja on May 6th and 7th, 2026. As part of the conference, the third edition of the CSEAN Capture The F...
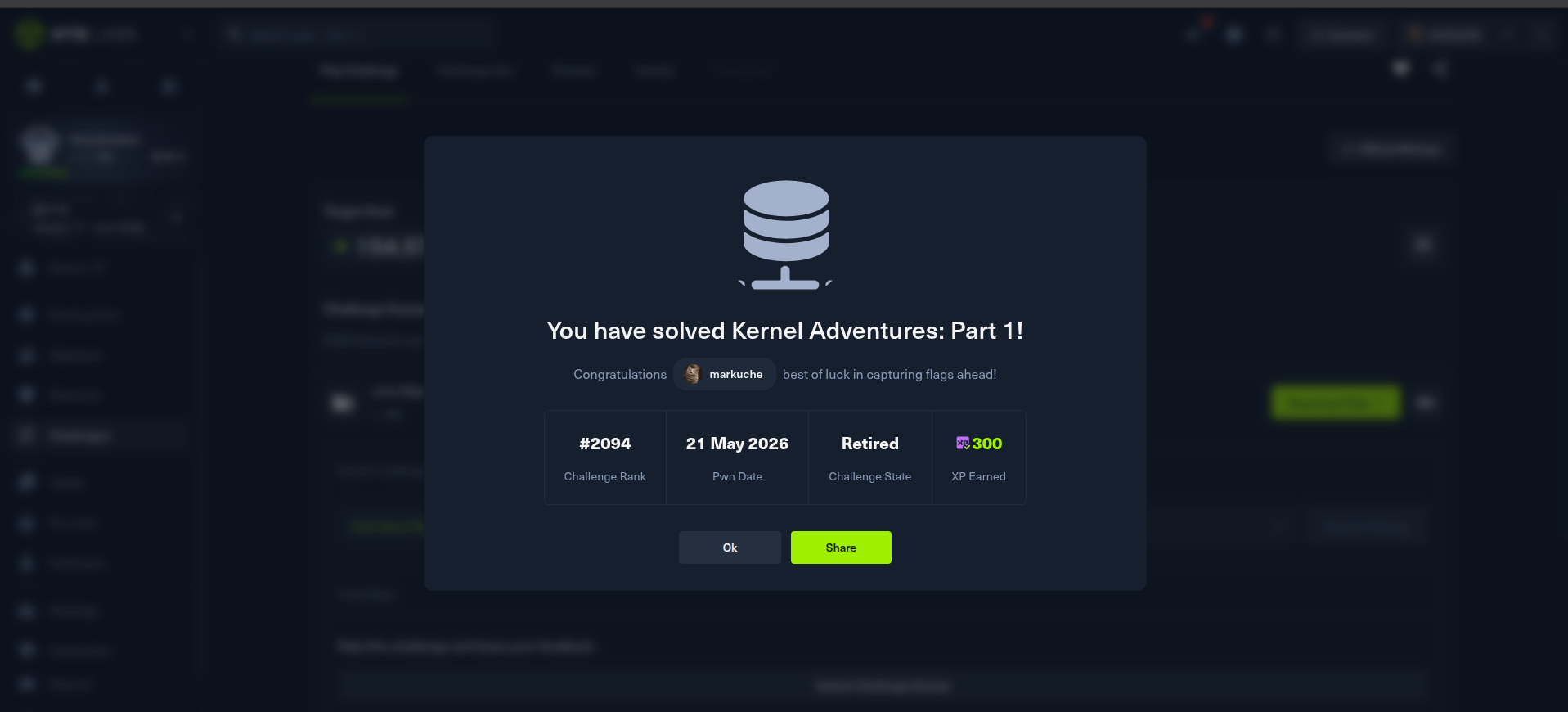
HackTheBox - Kernel Adventures 1 Overview Kernel Adventures: Part 1 is a medium-difficulty kernel pwn challenge focused on reversing a password verification routine and exploiting a double-fetch ...
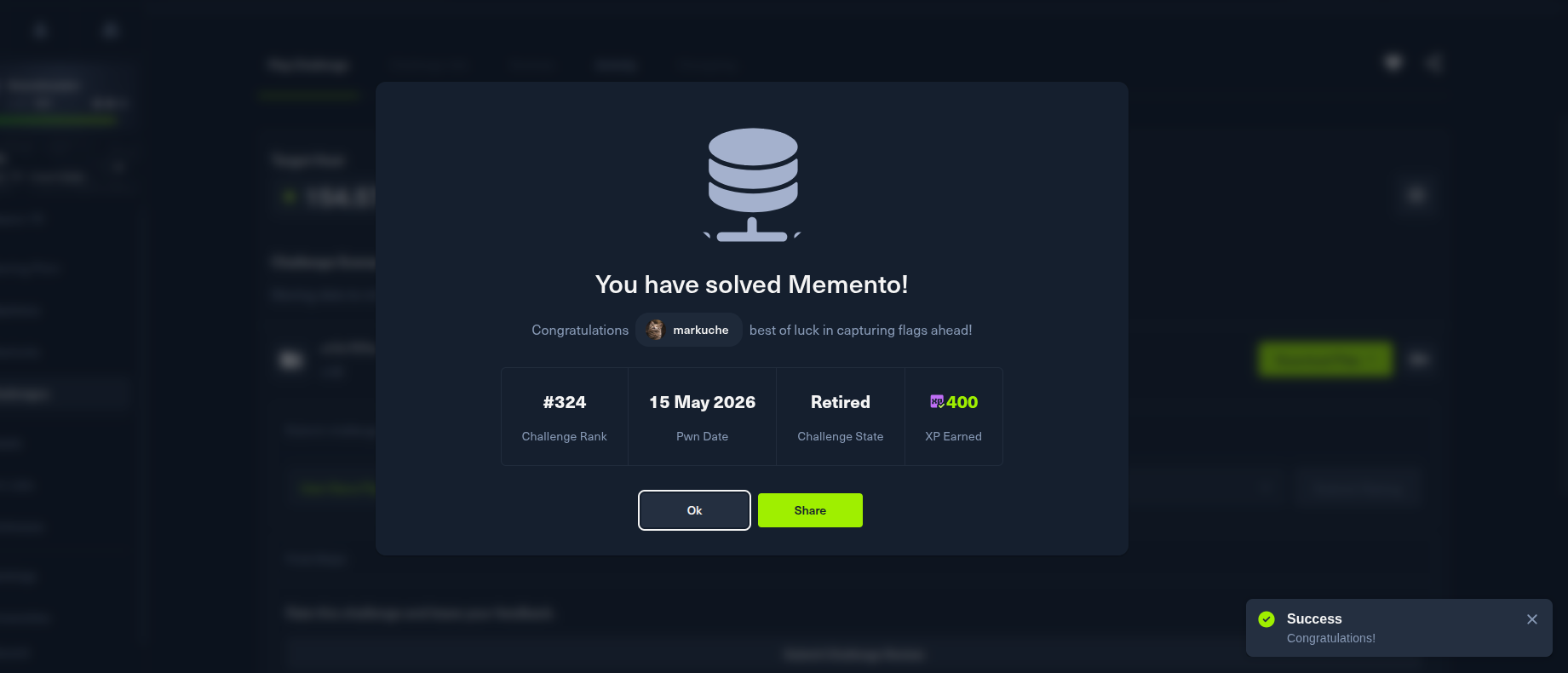
HackTheBox - Memento Background I decided to work on the Memento pwn challenge on Hack The Box after it was recommended, especially since it was set to retire in just two days. At first, I wasn’...
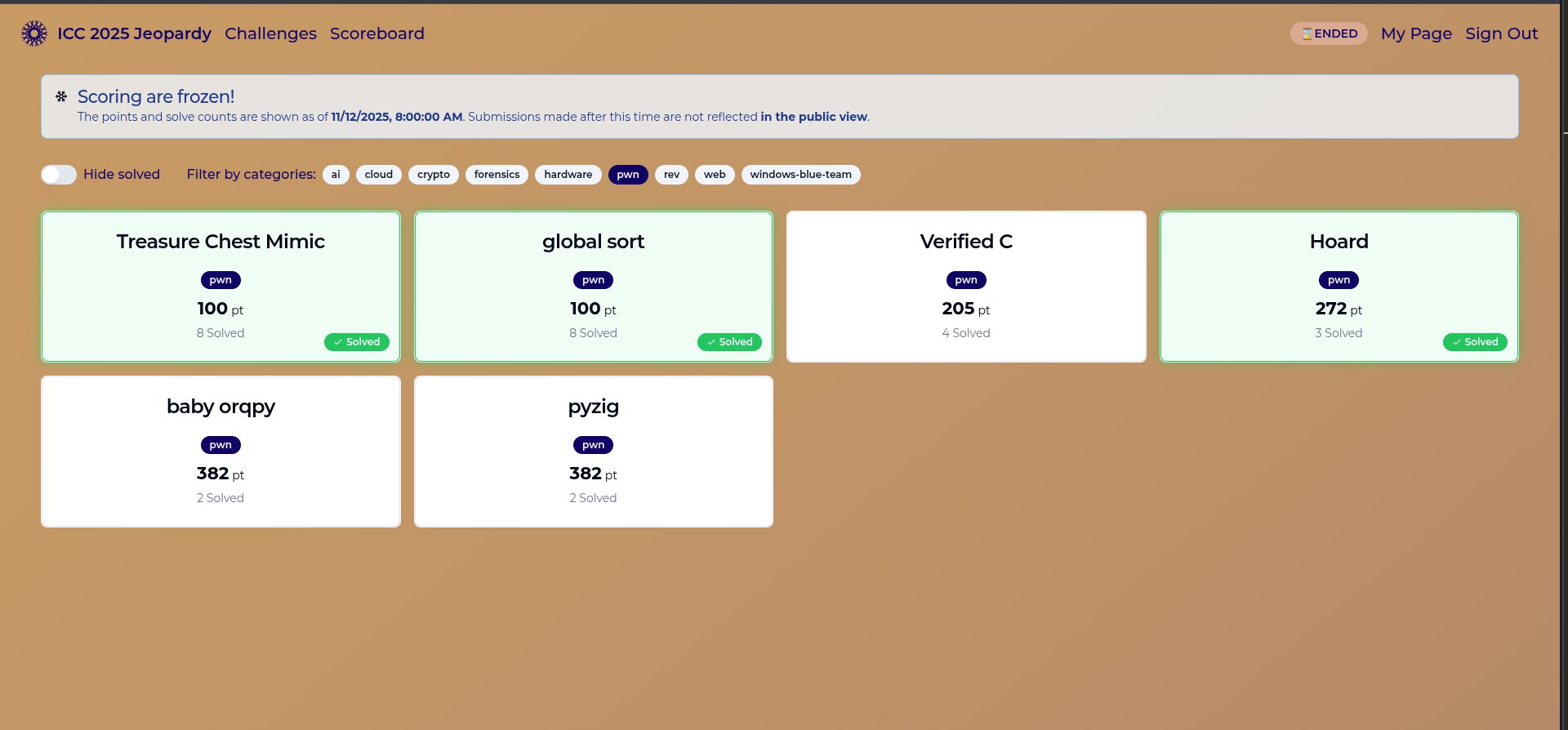
International Cybersecurity Challenge (ICC) - Tokyo Japan In this blog post, I’ll be sharing writeups for some of the challenges I solved during the International Cybersecurity Challenge (ICC). Th...
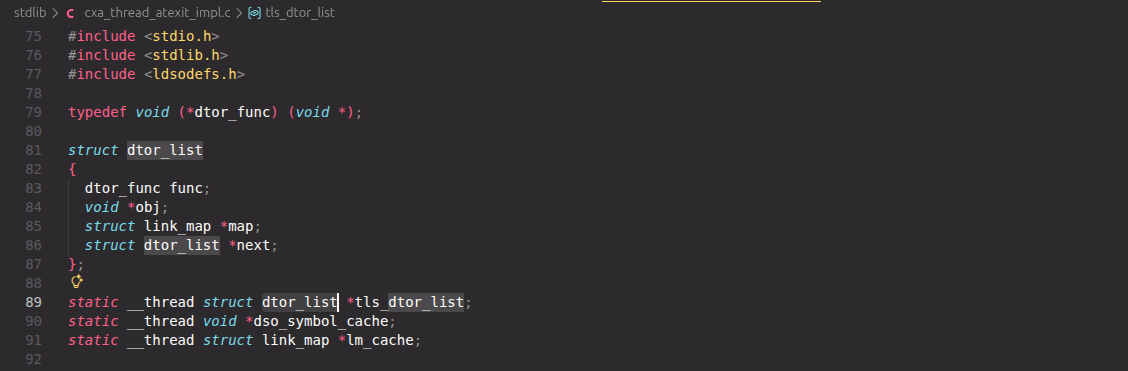
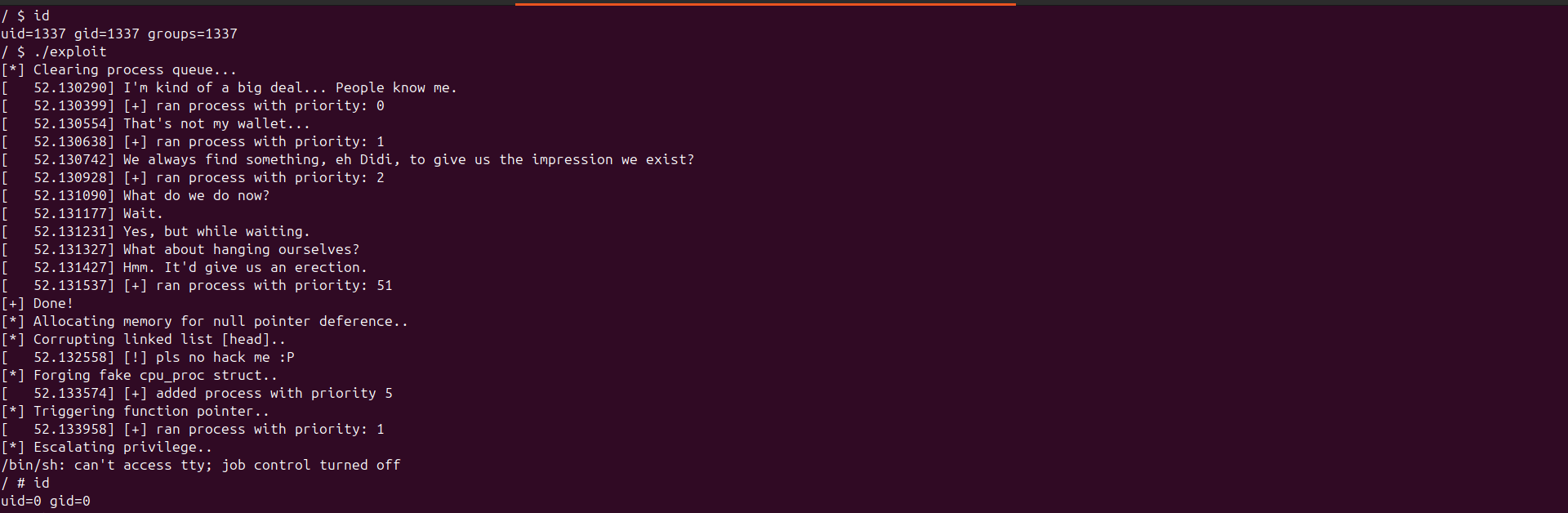
Gaining code execution via exit() Overview In this blog, we explore how code execution can be achieved during program termination by abusing the glibc exit() mechanism, specifically through TLS d...
RPISEC Kernel Exploitation Overview After watching the video on kernel exploitation, I decided to take things further by attempting chall1, the challenge provided by the organizers for viewers to...